In today’s digital age, cyber threats are becoming more frequent and sophisticated than ever before. According to the Verizon 2022 Data Breach Investigations Report (DBIR), 42% of the investigated breaches were due to stolen credentials. As a result, there is an increasing need for stronger authentication methods since traditional authentication methods, such as the combination of usernames and passwords, are no longer enough to protect sensitive information and systems from unauthorized access.
In this blog, we will explore how Advanced Authentication works, why using Advanced Authentication methods is the way forward and the benefits of implementing this more secure way of authenticating users.
What is Advanced Authentication?
Advanced Authentication is a cybersecurity approach that requires the use of additional security methods, beyond the traditional ones, to authenticate a user’s identity. Advanced Authentication makes it more difficult for hackers to gain unauthorized access to an organization’s accounts and information.
Advanced Authentication and Strong Authentication are often used interchangeably, but they are not the same thing. Strong Authentication refers to any authentication approach that combines two or more factors to verify identity (for example: one-time passwords, smart cards, hardware tokens, etc.).
Advanced Authentication is a more sophisticated approach. It goes beyond strong authentication by leveraging machine learning (or other advanced technologies) to assess the risk level of a login attempt and adjust the level of required authentication accordingly.
The implementation of Advanced Authentication can vary from one organization to another. Some organizations combine Multi-Factor Authentication (MFA) with behavioral analytics to achieve Advanced Authentication. Others may use adaptive authentication methods and perform a risk analysis of every login attempt to determine the extent of required security. Still others may use passwordless authentication methods to provide a much stronger level of security, making it harder for hackers to gain access. An increasing number of organizations combine two or more of these approaches together to further provide the best possible security.
Ultimately, the implementation approach will depend on a variety of factors, such as the organization’s regulatory requirements, the need for strong security hygiene practices and the availability of appropriate tools.
Is Multi-Factor Authentication (MFA) an Advanced Authentication method?
Whether or not MFA qualifies as Advanced Authentication depends on how it is implemented. MFA refers to any authentication approach that uses more than one verification factor. However, the sophistication and robustness of the factors can vary.
For instance, an MFA solution that uses behavioral validation as a secondary authentication factor may be considered an example of Advanced Authentication. However, an MFA solution that relies on a security question as a secondary factor would not meet the criteria for Advanced Authentication.
Ultimately, the level of security provided by an MFA solution will depend on the specific factors and technologies used, as well as how they are implemented and managed.
How does Advanced Authentication work?
Advanced Authentication relies on user verification methods that are less likely to be stolen or compromised by attacks like phishing or MFA fatigue. Advanced Authentication includes the use of two or more factors of authentication, such as something the user knows (i.e., a password, PIN or security question), something the user has (i.e., a physical token, smart card or mobile phone) or something the user is (i.e., biometrics – iris scan, fingerprint or facial recognition), plus the use of adaptive authentication and/or passwordless authentication.
Even though the specifics may differ, a typical Advanced Authentication process may involve the following steps:
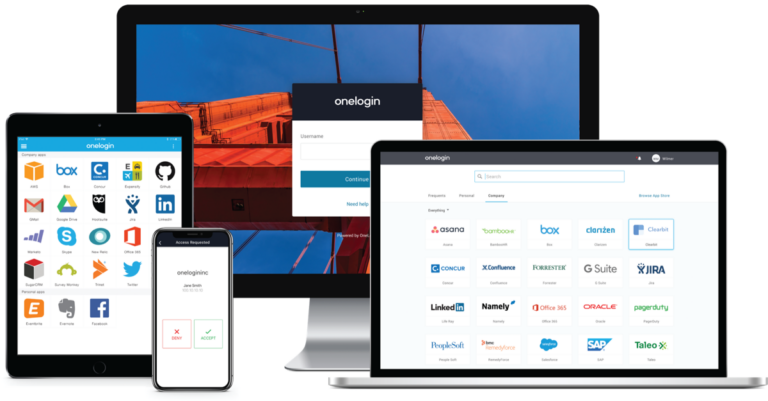
- A user tries to log in using a Single Sign-On (SSO) application, a desktop client or a web browser
- The authentication system analyzes different parameters of the authentication request to determine its risk level. For instance, the system may check if the user is logging in from the same device that they normally use, at their usual time and from a trusted network. If so, the request is marked as low risk. Otherwise, a higher risk score is attached to it
- For low-risk requests, the user may only be asked to provide one authentication factor, such as a one-time passcode sent to their authorized device
- For high-risk requests, the user may be required to provide multiple proofs of identity, such as a fingerprint, a one-time passcode or a security token
- If the validation is successful, the user is granted access. If it fails, access is denied and a security event is logged
- Frameworks used for Advanced Authentication
There are several frameworks and standards that can assist in enforcing Advanced Authentication:
- Client to Authenticator Protocol (CTAP1) is a standard that describes how a browser communicates with an external authentication device, such as a hardware security key
- OpenID Connect is a framework that verifies the identity of the end user based on the authentication performed by an Authorization Server, as well as to obtain basic profile information
- JSON Web Tokens (JWTs) are used for authentication and authorization purposes in web applications and APIs
- FIDO 2/WebAuthn is a framework that replaces passwords with FIDO 2.0 credentials that can’t be phished or replayed and are not subject to server breach attacks
User requirements to pass Advanced Authentication
The specific user requirements to pass Advanced Authentication may vary depending on the organization’s policies and the enforced authentication controls. However, in general, Advanced Authentication aims to provide a smoother login process for authorized users, while increasing the difficulty for a threat actor to gain access.
By utilizing AI-powered pattern detection and behavioral analytics, the authentication system can accurately distinguish between legitimate users and potential attackers. Authorized users can gain access through a quick and seamless one-step authentication process. Conversely, potentially malicious actors are required to pass through multiple layers of strict authentication controls to gain access.
Advanced Authentication tools
There are various kinds of tools available for Advanced Authentication:
- Multi-Factor Authentication (MFA) applications allow organizations to add layers of security to their authentication process
- Single Sign-On (SSO) tools with adaptive authentication can be used to increase both security and usability
- Passwordless authentication is an important part of an advanced authentication strategy as it can strengthen protection and improve the user experience by offering a more secure and convenient way to authenticate users
- Biometric authentication tools offer organizations the ability to authenticate users based on unique physical traits, such as fingerprints or retina scans
- Password and credential vaults are specialized applications designed to provide secure storage for sensitive information, such as passwords, API keys and other confidential data
Key benefits of Advanced Authentication
Advanced Authentication offers many benefits that significantly enhance security measures and protect sensitive company and customer information. The top five benefits of Advanced Authentication are:
- Enhances security
The primary benefit of Advanced Authentication is enhanced security. Advanced Authentication uses Multi-Factor Authentication, which can significantly strengthen security. By combining multiple factors, it becomes exponentially more difficult for unauthorized individuals to gain access. This added layer of security reduces the risk of identity theft, data breaches and unauthorized access
- Protects against password-based attacks
Password-based attacks, such as brute force, phishing and dictionary attacks, can be mitigated through Advanced Authentication methods. Advanced Authentication introduces more secure authentication methods, such as biometric scans or hardware tokens, which are not susceptible to common password-based attacks.
- Helps meet increasing compliance requirements
Given the rapid increase in breaches, many industries, such as health care and financial services, are facing increasing regulatory requirements for data privacy and security. Advanced Authentication is often a requirement for compliance with these regulations. Failure to comply with these regulations can result in financial penalties, reputational damage and other legal consequences.
- Improves user experience
While Advanced Authentication strengthens security, it also enhances user experience and productivity. Users no longer need to remember complex passwords or enter lengthy security codes. Instead, they can simply use their fingerprint or facial recognition to authenticate themselves. This results in a streamlined authentication process and improves overall productivity.
- Increases scalability and adaptability
Advanced Authentication solutions can be implemented across various platforms, including cloud-based services, mobile applications and on-premises systems. Whether it’s biometrics, smart cards or other authentication factors, Advanced Authentication systems can adapt to changing security landscapes, ensuring ongoing protection against emerging threats.
By implementing Advanced Authentication methods, organizations can effectively safeguard their systems, data and users, reducing the risk of unauthorized access and potential security breaches.