
OneLogin gives users the ability to access the applications and other resources they need to do their job by logging in once to a single interface. Platforms like OneLogin are known as Identity and Access Management (IAM) solutions that are primarily used to provide their users with a Single Sign-on (SSO) experience.
Think of a medieval worker coming to get their tools from within the castle walls.
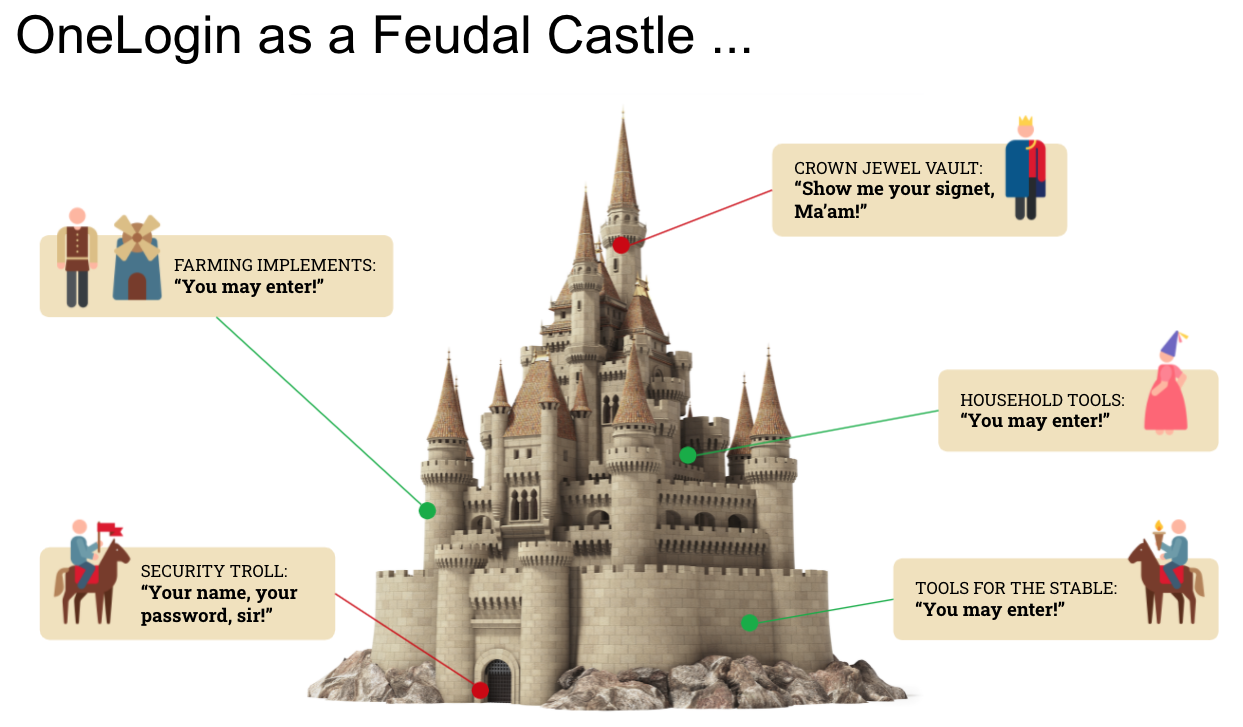
An old troll sits at the gate challenging workers for their name, a secret password and possibly a special item that only they have, like a medallion around their neck. The troll is needed in order to make sure that enemies don’t get into the castle. If the worker provides the correct information, they are let in.
Once the worker is within the castle, they can access the tools they need within various storage rooms: farming tools, stable tools, household tools, etc. Accessing these rooms is considered a low risk.
However, there are certain places within the castle that need extra protection like the vault that contains the crown jewels. To access the crown jewel vault, workers have to face yet another troll. The young lady whose job it is to retrieve pieces and bring them to the royal family is given a special signet ring. Without the presentation of that ring to this troll, she is not allowed entrance to the crown jewel vault. Accessing the crown jewels is considered a high-risk activity, so an extra security check is required.
OneLogin is analogous to the castle.
The troll at the gate represents a user security policy that requires users to provide their username, a password and an additional form of authentication. Once you provide this information, you are allowed into your OneLogin account.
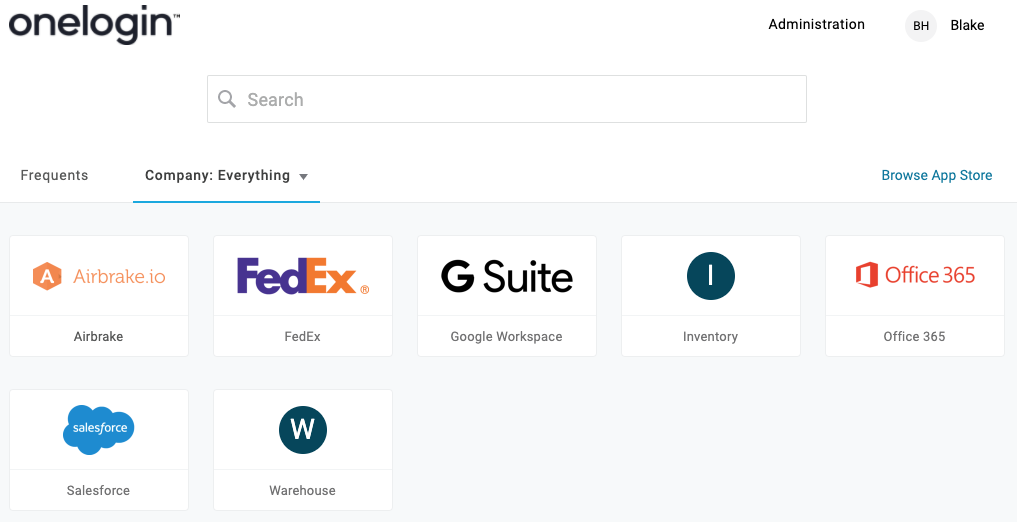
The tool rooms and crown jewels room represent the applications a user is assigned to within the OneLogin Portal. Once a user is in the portal they can easily access what they need without having to provide their credentials again.
The troll looking for a signet ring before entrance to the crown jewels is granted is akin to an Multi-Factor Authentication (MFA) token request from a software or hardware token. Further authentication is often desired for the most important and valuable apps.
OneLogin even provides its own secure “signet ring”: OneLogin Protect. OneLogin Protect is an authenticator app that can be used as a primary authentication factor or an additional authentication factor, not just with OneLogin, but with many other applications that support authenticator apps.

How Does OneLogin Work?
The analogy of the feudal worker entering the castle to retrieve what they need describes the experience OneLogin provides to end users. Behind the scenes OneLogin provides features to administrators that make controlling how users log in and what they can access once they log in as simply as possible. Administrators can configure OneLogin to automatically assign users to applications or different login requirements depending on the department they are in or their location or any other attribute that seems appropriate. By utilizing secure authentication protocols, administrators can reduce their attack surface exposure by eliminating the use of passwords as much as possible. They can even extend OneLogin to control access to WiFis, VPNs and Remote Desktop sessions.
Modern Day Security in a Feudal Landscape
Protecting your organization from breaches has become one of the highest priorities for IT/Security Departments. SSO solutions are no longer nice to have. They were considered nice to have because they provided users with a single interface to access their applications from instead of having to remember a bunch of different URLs, usernames and passwords. Solutions like OneLogin are now a must-have. IAM solutions like OneLogin not only provide a simple SSO experience for users, but they also utilize stronger authentication protocols to access the applications and provide multiple secure options to control access to the portal itself.

